Last month, General Chuck Yeager sued Airbus for violation of right of publicity, false endorsement, and trademark infringement. The basis of his complaint? In introducing its new Racer high-speed, cost effective helicopter, Air Bus referenced General Yeager’s breaking of the sound barrier at a press conference, and then repeating the reference on line and in print. Specifically, Air Bus said:
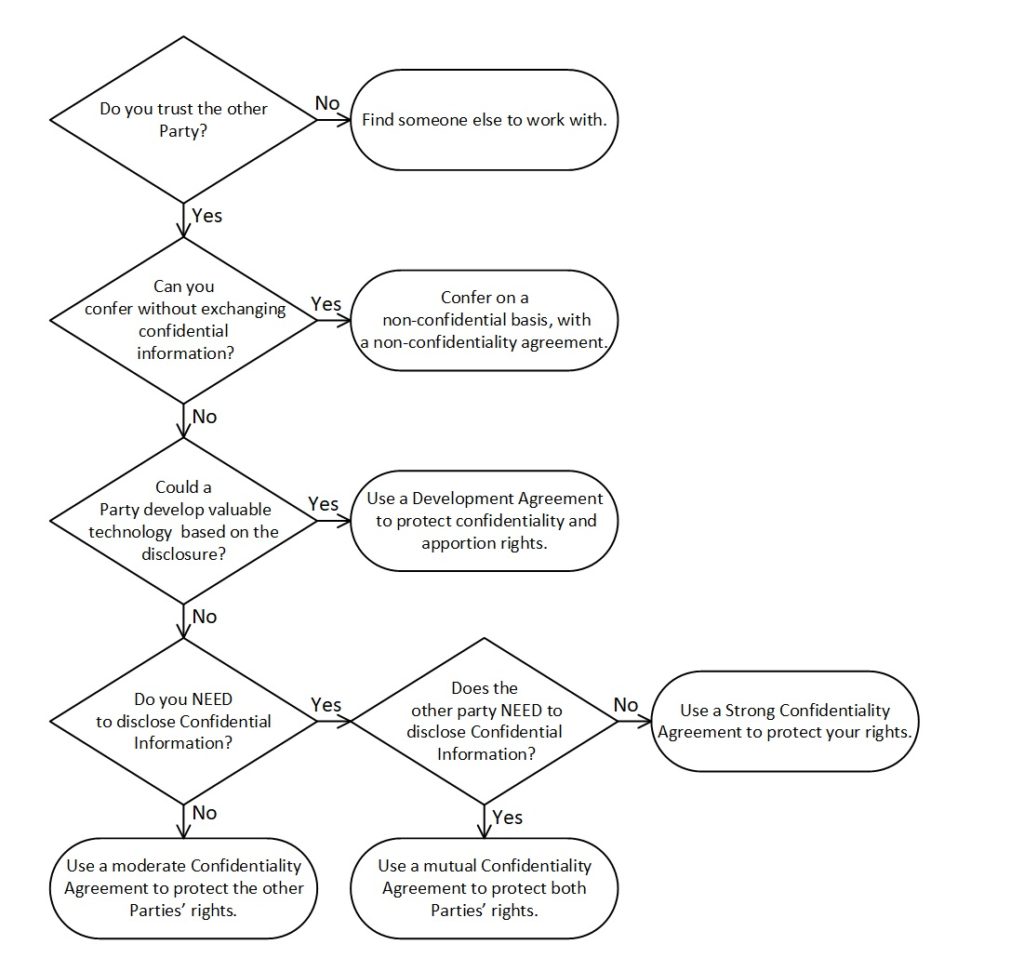
This seems little more than an innocuous reference to a historical fact. It adds some information and interest to an otherwise bland commercial statement, but it seems highly unlikely to cause anyone to believe that General Yeager is in any way connected with the Racer helicopter, let alone endorses it. Shouldn’t anyone, including a commerical entity, have the right to reference a historical event to make a point — at least if they do so in a way that doesn’t make it seem that they have the approval or endorsement of those involved in the event?
Unfortunately, the right of commercial speakers to reference historical events is not so clear. Had Air Bus been a slightly better student of history, it might of known that this is a lesson that General Yeager taught AT&T nearly a decade earlier. AT&T Mobility — then called Cingular — referenced General Yeager in an eerily similar press release:
To paraphrase George Santayana, those who don’t study history are doomed to repeat it. One might add that if you are commercial entity, even if you study history, you best not talk about it!